
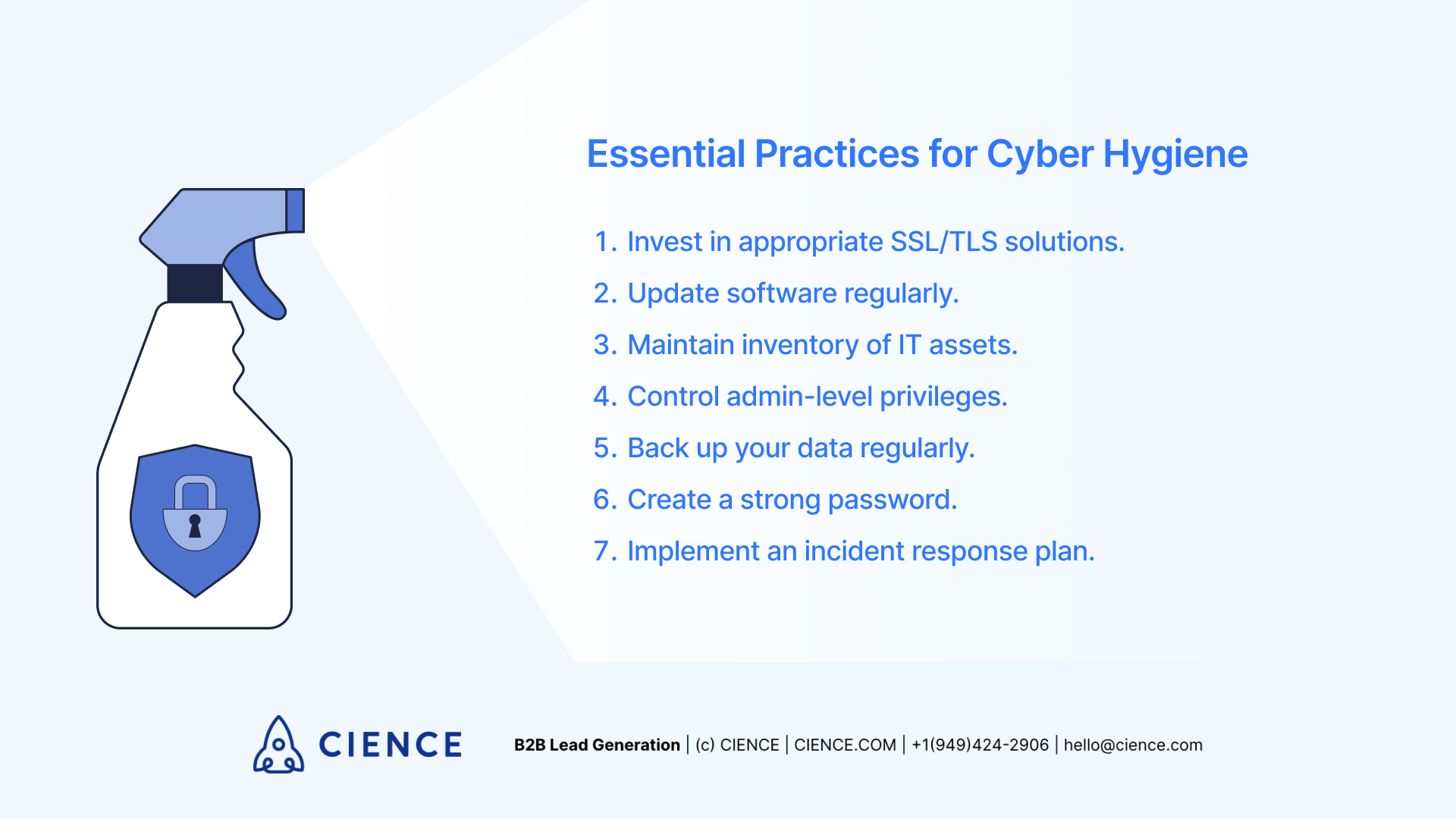
Cyber hygiene is the set of routine practices that protect networks and data from security breaches. Close to 80% of companies have experienced a cyber attack according to Verizon's DBIR. The 7 best practices include investing in SSL/TLS certificates, updating software regularly, maintaining IT asset inventory, controlling admin privileges, backing up data, using strong passwords, and implementing an incident response plan.
Last Refreshed: March 2026 with updated statistics and tool information.
Cyber hygiene is the set of routine practices and precautions that individuals and organizations follow to keep their data, networks, and systems secure from cyber threats. With close to 80% of companies having experienced a cyber attack, implementing strong cyber hygiene practices is no longer optional — it’s table stakes.
From Quincy Berg, SDR Operations Lead, CIENCE: “Cyber hygiene and data hygiene overlap more than most teams realize. When your systems hold thousands of prospect records — direct-dial numbers, firmographic data, buying intent signals — the security of those systems is as critical as the quality of the data itself. A breach isn’t just an IT problem; it’s a pipeline problem.”
Global companies face an average of 3,000 cyber threats per day, according to a report by McAfee and the Center for Strategic and International Studies (CSIS). With security breaches making headlines on a near-weekly basis, and with B2B data being more valuable than ever, it doesn’t matter whether you’re a private user or an enterprise — poor cyber hygiene leads to problems. The only question is severity.
The best way to address those problems isn’t to handle them after the fact. Good cyber hygiene begins well ahead of any potential threat — and that’s exactly what makes it effective. Preventative measures can stop security breaches before they get a foothold.
Whether it’s addressing existing security gaps or being mindful of sensitive data on your network, good cyber hygiene practices aren’t difficult to understand or implement. This guide explains how to build a strong security posture by covering the seven best practices you should adopt today.
7 Best Practices to Maintain Cyber Hygiene
According to the Verizon Data Breach Investigations Report, close to 80% of companies have experienced a cyber attack. As organizations increasingly rely on digital technology and B2B data to run their operations, keeping cyber hygiene current is not a nice-to-have — it’s a business requirement.

To protect your digital assets and data from cyber threats, follow these seven critical steps:
1. Invest in appropriate SSL/TLS solutions.
Encryption is the baseline for every modern network, whether local or global, large or small. Without it, no downstream hygiene practice has a secure foundation to build on — and a webmaster needs to know which SSL/TLS product to invest in before anything else.
Choosing an SSL certificate isn’t glamorous, but it is necessary. While the options can seem overwhelming, leading SSL certification providers have expert teams ready to help you identify the right SSL/TLS certificate for your specific use case.
Beyond patching critical vulnerabilities across web browsers and mobile devices, SSL certification also helps growing businesses by improving their SEO and extending their audience reach organically. It’s the strongest starting point for any serious cyber hygiene program.
2. Update software regularly.
Keeping your software fully up to date is essential — and for more reasons than new features. What matters from a security standpoint are the monthly security patches that defend against newly discovered vulnerabilities.
The equation is simple: malicious software is actively developed every day. Your antivirus applications and operating systems need fresh malware definitions and security patches as often as possible to continue detecting threats efficiently. Modern cybersecurity tools handle much of this in the background — but automated updates only work if they’re enabled.
More specialized enterprise-grade software needs security updates even more frequently than user-facing apps. Don’t wait for the prompt. Schedule it.
3. Maintain inventory of IT assets.
Managing and maintaining your IT asset inventory is a critical task that’s easy to defer until it’s too late. IT assets go out of date, carry recurring fees, and expire — and you don’t want to discover a lapsed security subscription during an active breach.
IT asset management also reduces financial and compliance risk. Software audits expose significant liability when inventories aren’t current. Keeping track of what you have internally is foundational to keeping your operations secure and your risk exposure manageable.
Your network faces 3,000 cyber threats every day. Your data is either protected — or it’s a liability waiting to be realized.
Talk to a Data Security Expert →
“The partnership paid for itself — and then some.” — Capacity, SaaS
4. Control admin-level privileges.
An organization’s ability to protect sensitive data is only as strong as the people controlling its security systems. Security software runs itself in most cases — but administrators are the ones who keep the whole operation at spec.
Controlling who holds admin-level privileges is one of the most consequential security decisions you’ll make. Administrators have the power to substantially alter your backend operations, and no antivirus software can stop a malicious or careless insider. That’s a threat that bypasses every technical safeguard.
Cyber hygiene best practices consistently emphasize that administrators must be reliable, vetted individuals with the organization’s best interests at heart. Access control is the one safeguard that operates above every other layer of security.
5. Back up your data regularly.
Running regular data backups might not seem as urgent as SSL/TLS investment — but data loss is one of the most disruptive failures an organization can face. And it doesn’t always come from a malicious actor. Media corrupts. Systems fail. Natural disasters happen.
Regular backups mean you always have a fallback when things go wrong. A healthy backup setup includes both on-site and off-site copies, with coverage as broad as operationally feasible. The goal is to make momentary data loss a recoverable inconvenience, not a business-ending event.
CIENCE works with 2,500+ B2B clients across 250+ industries to build and protect the data infrastructure that powers outbound pipeline. Clean, backed-up data isn’t just a security asset — it’s a revenue asset. Rated 4.6/5 on Capterra by verified users.
6. Create a strong password.
Passwords are a mandatory element of cyber hygiene at every level. And while it might seem like a strong password won’t help much once credentials are leaked — that framing misses the point. Complex, varied passwords raise the cost of unauthorized access significantly, even after a breach.
On top of using services like haveibeenpwned.com to monitor credential exposure, users serious about cyber hygiene should use complex, unique passwords for every service they access. A strong password has these characteristics:
- 12 characters minimum
- Mixed alphanumerics
- Lowercase and uppercase letters
- At least one special character (e.g., ? or !)
Password managers have become the practical standard for managing this complexity — and for good reason. Research which option fits your use case and threat model before committing.
7. Implement an incident response plan.
When a security incident escalates, no plan means chaos. A pre-built incident response plan provides a specific, step-by-step set of instructions that enables fast containment and recovery — and dramatically reduces the financial, legal, and reputational damage of any breach.
According to the SANS Institute’s Incident Handlers Handbook, every proper incident response plan should include six steps:
- Preparation
- Identification
- Containment (short and long-term)
- Eradication
- Recovery
- Summary
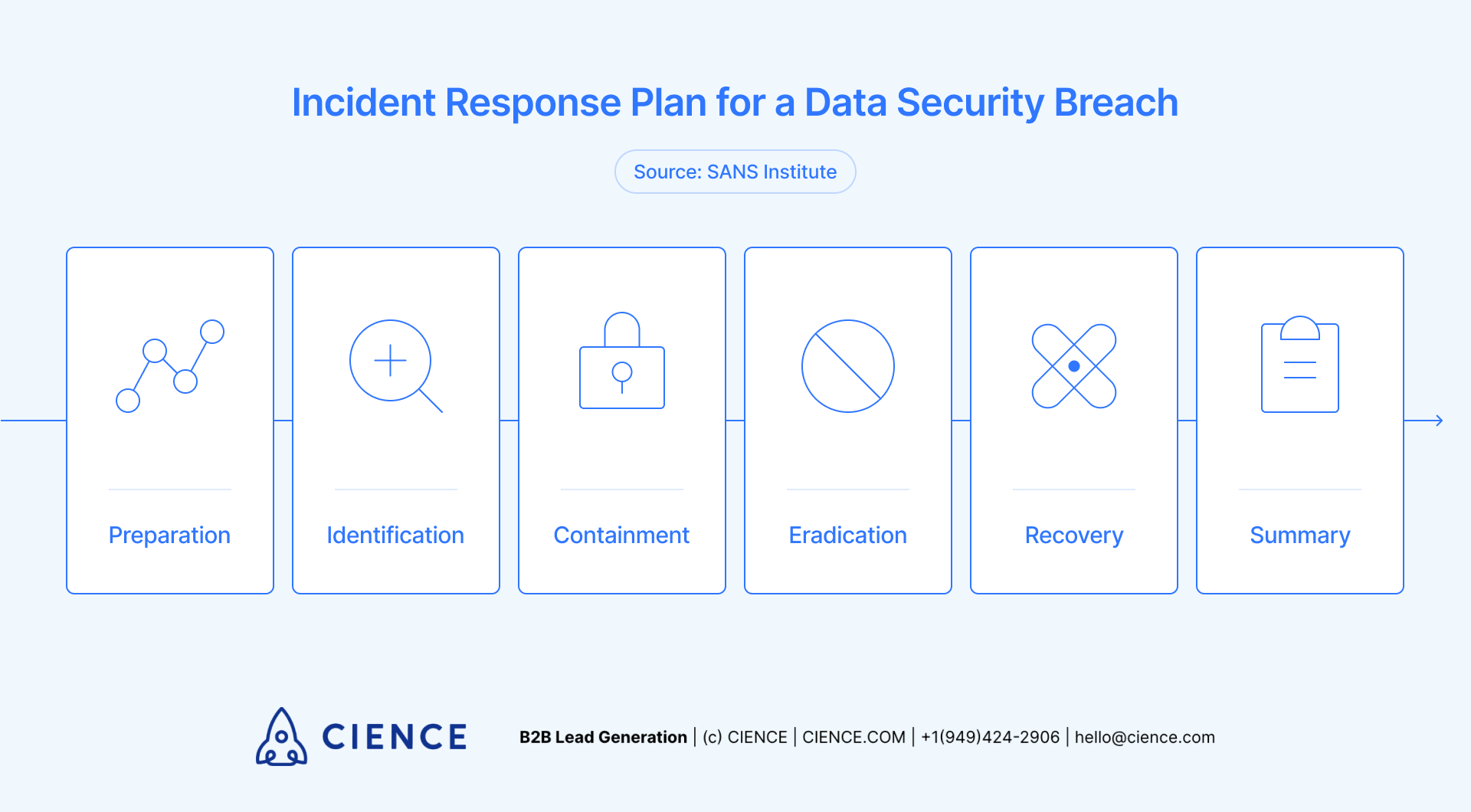
A full incident response plan is an essential component of corporate cyber hygiene. Even individual users benefit from having a simple, personal set of baseline instructions ready. Better to have it and not need it.
Keep Your Network Secure with Cyber Hygiene
By establishing a consistent cyber hygiene routine, you protect your data from the vast majority of threats before they escalate. No security system is unbreachable — but a motivated attacker is far more deterred by an organization that has followed these practices than one that hasn’t.
Basic cyber hygiene reduces your attack surface and improves your posture against both opportunistic and targeted threats. By adopting strong practices around your sensitive data and staying mindful of your security posture, you prevent incidents before they ever take place.
CIENCE helps B2B companies across 250+ industries build the data infrastructure and outbound programs that power sustainable pipeline growth. When your data is clean, secure, and current, it doesn’t just protect you — it compounds.
Bad data doesn’t just waste budget — it trains your team to accept poor results as normal. Clean intelligence changes everything.
There’s no reason to make yourself a soft target. Identify vulnerabilities today to prevent network breaches tomorrow. Security awareness is crucial in every context, and strong cyber hygiene raises the floor for your entire organization.
“They definitely supersede our internal capabilities.” — Candice Long, Marketing Director, Learning Ally
CIENCE + graph8 pricing: $5,000 one-time GTM system setup, $2,499/mo strategic execution, and the graph8 platform at $499/mo. No long-term contracts. See full pricing →
Whether or not you decide to work with us, you’ll walk away with a clear picture of where your pipeline is leaking and what it would take to fix it.
Frequently Asked Questions
What is cyber hygiene and why is it important?
Cyber hygiene refers to the routine practices that individuals and organizations adopt to maintain the health and security of their digital systems, networks, and data. It is important because global companies face an average of 3,000 cyber threats per day, and preventative measures like regular software updates, strong passwords, and data backups can stop most breaches before they occur.
What are the most common cyber hygiene mistakes?
The most common mistakes include using weak or reused passwords, failing to update software and operating systems promptly, not backing up critical data regularly, and granting too many users admin-level privileges. According to the Verizon DBIR, human error and credential compromise remain the leading causes of security breaches in organizations of all sizes.
How often should I update my cyber hygiene practices?
Software and security updates should be applied as soon as they are released, ideally through automated patch management. Data backups should run daily for critical systems, and IT asset inventories should be reviewed quarterly. Incident response plans should be tested and updated at least annually, or whenever significant changes to your infrastructure occur.
A graph8 company — AI-powered GTM execution across 250+ B2B industries.
graph8 Platform
From $499/mo
Run your own GTM campaigns with AI-powered data, sequences, and analytics.
Start Free — 2,500 Credits No credit card requiredCIENCE Managed
From $2,499/mo
Our GTM teams build and run your outbound campaigns end-to-end.
15-min call · No commitment2,500+ B2B companies served · Month-to-month contracts · See full pricing →
